Application Layer – Telnet , P2P file sharing and Rlogin (Remote Login)
Moving forward in this series of application-layer features, we will now look into some other important characteristics of this layer. In the previous post, we have seen complete detail about the HTTP protocol and its usage.
Undoubtedly we can say that in today’s world ,the most popular (indispensable) applications are remote logging, file transfer, and mail services. So now we will explore each of these terms i.e. ‘Telnet’ , ‘P2P file-sharing’, and ‘Remote Login’ in detail.
What is Telnet ?
Telnet is a client server program to login to remote systems. It uses TCP/IP protocol and underlying communication can take place through PSTN, Satellites etc. In any timesharing environment, users are part of the system with some right to access resources.
Each authorized user has identification and also a password. The user identification typically defines the user as part of the system. To access any system, the user logs into the system with user id or log-in name. The system also includes password checking to prevent an unauthorized user from accessing the resource.
Telnet allows you to login to the system for any operation (OS commands and program execution) and FTP is used only for file transfer files. The action consists of establishing a connection, comparable to a connection via telephone. Your terminal connects to the server on the other computer and is able to give actions (input), and receive data in return (output).
Telnet is used for a number of activities such as checking email at another account, other on-line services, or perhaps an internet BBS, in addition to many other possibilities. In addition to machines across the net that are accessible, each machine has a number of ports that offer different types of access to the system.
As with any other type of travel the key part of beginning your adventure is to know something about where you are going or want to go. To use Telnet you need a specific address, however, now it is possible to access Telnet .
Connections through hyperlinks on the web, this means that browsing and stumbling across something that you are interested in is possible. Telnet is an application used on the internet to connect to a remote computer, which enables access to the computer and its resources.
Telnet Login
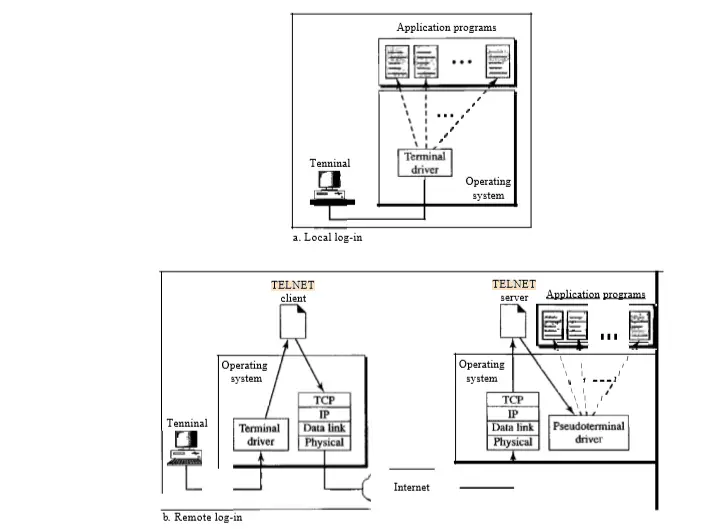
When a user logs into a local timesharing system (it is a technique which enables many different people, located at various terminals, to use a particular system at the same time), it is called local log-in. As a user types at a terminal or at a workstation running a terminal emulator, the keystrokes are then accepted by the terminal driver.
The terminal driver then passes the characters to the operating system. The operating system further interprets the combination of characters and invokes the desired application program or utility. When a user wants to access an application program or utility located on a remote machine, she performs remote log-in.
Here the TELNET client and server programs come into use.All uses of Telnet begin with the designation of a destination, an address that you want to go to a computer to be accessed. Although it is possible to take the direct route by telneting directly to the intended destination.
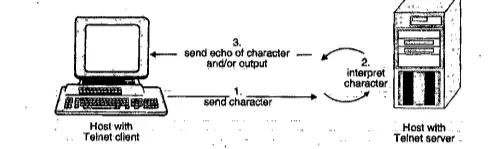
The user also sends the keystrokes to the terminal driver, where the local operating system accepts the characters but doesn’t interpret them.
The characters are sent to the TELNET client, which transforms the characters into a universal character set called network virtual terminal (NVT) characters (NVT uses two sets of characters, one for data and the other for control) and delivers them to the local TCP/IP protocol stack.
TELNET uses only one TCP connection. The server also uses the well-known port 23, and the client uses an ephemeral port. The same connection is used for sending both data and control characters. TELNET accomplishes this by embedding the control characters inside the data stream.
However, to distinguish data from control characters, each sequence of control characters is preceded by a special control character called interpret as control (lAC).
What Is Remote Login (Rlogin)
Any user may want to run application programs at a remote site and create results that can be transferred to their local site(most common scenario). For instance, students may want to connect to their university computer lab from their home to access application programs for doing homework assignments or projects.
One way to satisfy that demand and others is to create a client/server application program for each desired service. We already have specific client-server applications such a FTP (file transfer protocol) , SMTP (mail protocol),etc .
But we need a more generalized client-server application to meet every user’s needs such that the user can access any application program on a remote computer, in other words, allow the user to log on to a remote computer.
Let us now understand some functions of Remote Login :
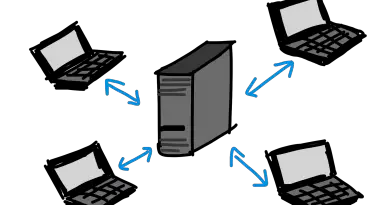
This is nothing but a remote access program. In a system if all users log into the central server computer and use its resources, it is known as Local login. In timesharing systems, it works well.
But sometimes a user may have to access an application program that is located on a computer which is not part of the local network. Such a computer is called a remote computer.
This user logs on to the remote computer in a process called remote login. A user specifies the IP address for selecting a remote server. It establishes a Telnet session.
Telnet is mainly a remote login protocol for executing commands on a remote host. The Telnet protocol runs in a client -server mode and uses the TCP protocol for data transmission.
A client then initiates a Telnet session by contacting a Telnet server at a remote host.
Recently, the use of Telnet in public networks has been discouraged since Telnet does not offer good protection against third parties that can observe (“snoop”) traffic between a Telnet client and a Telnet server.
The mode of operation includes telnet client and server. At the Telnet client, a character that is typed on the keyboard will not be displayed on the monitor, but instead, it is encoded as an ASCII character and transmitted to a remote Telnet server.
At the server, the ASCII character is first interpreted as if a user had typed the character on the keyboard of the remote machine. If the keystroke results in any output, this output is encoded further as the ASCII text and sent to the Telnet client, which displays it on its monitor.
The output can be just the (echo of the) typed character or it can also be the output of a command that was executed at the remote Telnet server.
Rlogin is an alternative remote login application program for hosts that run the Unix operating ‘system. Rlogin takes advantage of the fact that both the client and server run a similar operating system, and for this reason, it is simpler than Telnet.
P2P File Sharing (process to process file sharing)
We have already covered this feature (file sharing) of the application layer in detail in our previous posts. Now we will see the basic working of this application with the help of one example.

P2P file-sharing means a process to process file sharing.
The P2P file sharing is the most important Internet application because the highest amount of Internet traffic, corresponds to the P2P file sharing.
Modern P2P file-sharing system shares MP3 (3 to 8 Mb), videos (10 to 1,000 Mb), images, software documents etc.
In this section, we will discuss the protocols and networking issues in P2P file sharing.
Before going into details of P2P file-sharing system, let us take an example. Suppose Sam uses the P2P file-sharing application for MP3 downloading. He runs the P2P file-sharing software on his home PC (peer). He uses an ADSL connection to access the Internet. He shuts down his PC every night and does not have a hostname. So every time he connects to the Internet the ISP will assign a new IP address to his PC.
Suppose that Sam is connected to the Internet and searching for the MP3 for a particular song of a particular artist.
As soon as he goes into search, the P2P application displays a list of those peers who are currently connected to the Internet and have a copy of that song, for sharing.
Each one of them is an ordinary PC owned by an ordinary internet user like Sam.
Sam then requests the required MP3 file from one of the peers say Kate’s PC. Then a direct TCP connection gets established between Sam and Kate’s PC and the MP3 file is sent from Kate’s PC to Sam’s PC.
If Kate disconnects her PC from the Internet in the middle of this download, then Sam’s P2P file sharing software may attempt the remaining part of the MP3 file from the other peer.
Also when the download from Kate to Sam is going on, some other users can download some other songs from Sam’s Pc.
Thus the P2P file sharing allows direct sharing of information without any independent server getting involved. However P2P file sharing operates on the client-server principle. The requesting person acts as a client and the requested user acts as the server. The file is sent using the file transfer protocol (FTP).
In P2P file-sharing system, typically a large number of users are connected to the Internet and each user has objects such as MP3, videos, software, and images for sharing.
In the next post we will look into the basic details associated with any ISP (internet service provider). So stay tuned.
Aric is a tech enthusiast , who love to write about the tech related products and ‘How To’ blogs . IT Engineer by profession , right now working in the Automation field in a Software product company . The other hobbies includes singing , trekking and writing blogs .