Application Layer (email services) – Message Access Agents (POP and IMAP)
From the last few posts, we have been looking into the technical functionalities associated with the email services (that we use every now and then). So in this post, we will further dig deep into the retrieval process of the email messages from the server into the client’s system.
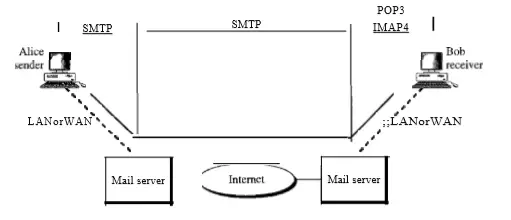
We already saw the details about SMTP protocol(message transfer agent) and User-agent.Now we will explore the message access agents used in this process. Before we proceed you may refer to the below figure for better clarity.
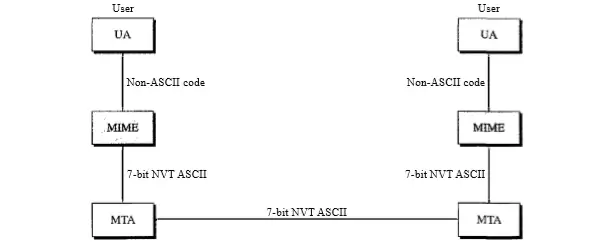
The first and second stages of the mail delivery system (refer diagram above) mainly uses the SMTP protocol. Nevertheless, SMTP just isn’t found in the third stage because the SMTP is basically a push protocol, it thus pushes the message data from the customer (client-side) to the server host that is required.
In simple terms, we can say that the way (direction of the movement) associated with the bulk data (a stream of data messages) is from the client to the respective destination server. On the other hand, the third stage finally needs a pull protocol , the client should poll the messages from the server-side(retrieval of mail messages).
The flowing movement of any group of data is normally from the server-side to the specific host device (client). The third stage thus uses an MAA (message access agent) .
There are two message access agents available , they are as follows :
- Post office protocol, version 3 (POP 3)
- Internet mail access protocol (IMAP 4)
(refer figure above for exact implementation position of these protocols in any email application process).
Post Office Protocol 3 (POP version 3)
Post office protocol (version 3 also called POP3) is simple and has limited functionality. The customer (client) POP3 software is initially installed on the PC that is a receiver, the host (server) POP3 software is further set up within the mail server (POP3 basically is made of both the software i.e. client POP3 plus the server POP3).
Mail access first begins with the client when the individual user (client) is required to download an e-mail from the mailbox present in the mail server. In this case the sequence of events as per the following manner :
- The client (user) establishes a link using the host server on the TCP slot 110..
- Then the client will send its user name and the password to the server in order to access the mailbox.(eg Gmail login)
- After successful authentication, the user can now able to access the mailbox. The user can then finally list and recover the respective mail messages, each at a time.
Modes of POP 3 :
POP 3 protocol has two modes of operation :
- Delete mode and
- Keep mode
Delete mode : In this specific model the mail will be deleted from the specific mailbox after each retrieval. The delete mode is most commonly used when any user is working at her/his PC and can save and furthermore organize the received mail message after reading or replying the same .
Keep mode : The keep mode is generally used when any user accesses the mail message away from that of the primary computer (e.g. a PC or laptop). The mail is then read and kept in the system for later retrieval.
Demerits of POP 3 :
- The user can’t create different folders on the server . The user also can’t able to view the partial contents of the email before downloading.
Internet Mail Access Protocol 4 (IMAP version 4)
Another mail access protocol is the Internet Mail Access Protocol (pull protocol), version 4 (IMAP4). IMAP4 is very similar to POP3, but it normally has many more features. IMAP4 is much more powerful and a bit more complex. This is ideal for users having multiple computers such as laptops in the office, PC at home etc.
A user can finally look for the email header ahead of downloading the message. IMAP basically creates a central repository that can be further accessed from any machine.
Thus it doesn’t copy email to the user’s personal machine. A user may able to partially download any e-mail. This is especially of good use in the event that bandwidth is very limited plus the e-mail particularly contains multimedia with very high bandwidth needs .
Additional features of IMAP 4 :
- It is possible for the user to create, rename or delete mailboxes on the mail server.
- Users can able to search the required contents of the email before downloading.
- A user can also able to create a sequential hierarchy of the mailboxes in any folder for a mail storage .
- User can able to partially download the email.
you can refer the below table for comparison between the two pull protocols :
| Sr No | Parameter | POP 3 | IMAP |
| 1 | TCP port used | 110 | 143 |
| 2 | email can be read | offline | online |
| 3 | multiple mail boxes | not possible | possible |
| 4 | partial message downloads | No | Yes |
| 5 | who backs up the mailboxes | User | ISP |
Web based Mail
There are some websites that provide email services to any user who accesses the site, for e.g. Yahoo and Hotmail. In this case, the mail will be transferred from the sender to the mail server via HTTP (will be explained in later posts) .
The message transfer from the sending mail server to receiving mail server will be done by SMTP protocol. Then in the final phase (pulling of the mail from the server to the client’s system ) will be carried out by HTTP (and not by POP or IMAP).
When the receiver sends a message to website, the user can then able to retrieve the mail. The website sends a log in form to the recipient (containing log in name and password).
If the credentials given by the user match correctly, then the email is transferred from the website to the receiver in HTML format.
So finally we are done with a complete understanding of the email services functionalities (how the message transfer/pulling really work) .
For the other two posts in this series, you may directly view User agents and SMTP post here.In the next post we will see the next interesting application of application layer i.e File sharing using the FTP protocol. So stay tuned..
Aric is a tech enthusiast , who love to write about the tech related products and ‘How To’ blogs . IT Engineer by profession , right now working in the Automation field in a Software product company . The other hobbies includes singing , trekking and writing blogs .