Azure Virtual Networks – The Ultimate Guide !! (Network Services By Azure In Cloud Computing)
If you really want to know the overview of the Azure Virtual Networks , then you are certainly in the right place .In this post, we will explore every basic detail of the Azure Vnet (virtual network) here . So just sit back and read further . We will first start with the basics and then proceed towards complex traffic management capabilities by Azure VNet .
What is Microsoft Azure?
Microsoft Azure is a set of unified cloud services, which help IT professionals and developers to build , deploy and manage applications through the global network of Azure data centers.
What Is Azure Network Services ?
Microsoft Azure Network Services offer the foundation for developing hybrid cloud solutions with the help of following essential resources.
Azure Virtual Network: Isolated network within the Microsoft Azure cloud.
Azure Traffic Manager: Controls how user traffic is distributed between geographies in cloud services.
Name Resolution Service: For internal hostname resolution within a cloud service.
Azure ExpressRoute: Extend on-premises networks into the virtual network over a dedicated private connection facilitated by a connectivity provider.
Application Gateway: works at the application layer and acts as a reverse-proxy service, terminating the client connection and forwarding requests to back-end endpoints.
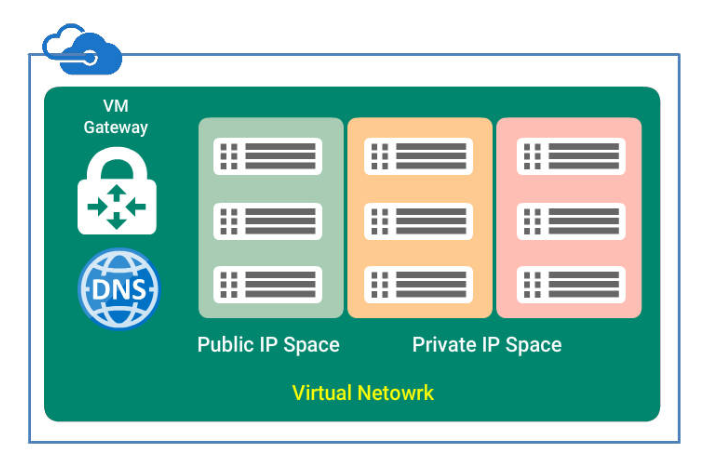
What is Virtual Network (VNet) ?
Virtual Network, also known as a VNet constitutes a logical boundary defined by a private IP address space that you designate. You can distribute IP address space into one or more subnets .This makes it functionally equivalent to on-premises networks.
VNets are similar to AWS VPC (Virtual Private Cloud), offering various networking features like the ability to customize inter-VM connectivity, Virtual Private Networks (VPN), access control, DNS, routing, and DHCP blocks.
Why We Need A Virtual Network ?
Azure Virtual Network allows to securely connect cloud infrastructure to your on-premises datacenter.
Virtual Networks allow to set up a virtual lab in the cloud by enabling connectivity to on-premises resources with the help of Point-To-Site and Site-to-Site VPN connections.
Virtual Network also acts as a DHCP server, which allows configuring a DNS server to be leased out when a virtual machine is a spin up in the cloud.
In this post you will learn how to plan and configure Azure Advanced Network(NW) services like,
- IP Addresses, Subnets & Azure DNS
- Azure LoadBalancers,Traffic Manager and Application Gateway
Now let us first start by understanding some basic terms first . Without wasting further time , let’s start.
Planning Vnets In Azure Virtual Network !!
Planning of Vnets is equivalent to planning the network in On-Premises networking components which includes,
- IP Address Space and Subnets
- Private IP Range and Public IP addresses
- Static and Dynamic IP addresses
- Azure DNS
Now we will understand this one by one :
IP Addresses Space
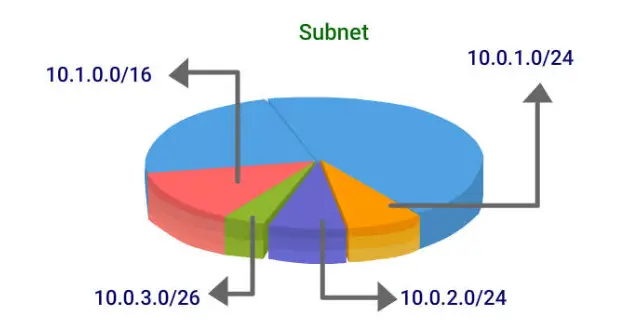
A Vnet allows organizations to design IP space in the Vnet, including breaking the IP space into virtual subnets.
IP addresses are assigned to Azure resources like VMs, application gateways, and load balancers,
By connecting through the IP Addresses, Azure resources on the same cloud can communicate with each other as well as on another cloud through the internet or on-premises network.
Address space of the Vnets can be further divided into smaller networks by using Subnets
Features:
- It provides logical and security isolation of Azure resources.
- VMs and PaaS role instances deployed to subnets (same or different) within a VNet can communicate with each other without any extra configuration.
- You can also configure route tables and NSGs to a subnet
CIDR Subnet Definition
CIDR (Classless Interdomain Routing) notation represents an IP address range by combining an IP address through its network mask. CIDR is the routing system that is now used by all gateway routers.
CIDR subnet definitions determine the number of bits in the IP address that defines the network.
For example: Consider 216.0.131.0/22 and its in binary representation 11011000.00000000.100000|11.00000000
- The network address can be defined as first 22 bits of an IP address i.e network mask of 216.0.128.0.
- Remaining 10 bits are for specific 258 host addresses.
IP Addresses Space Planning
While creating a VNet, the scope of IP addresses that can be allocated for the network resources is also defined. A VNet can contain both private and public IP address spaces.
- The communication with an Azure virtual network(Vnet) and the On-premises with a VPN configured is done by Private IP address
- The communication within the Internet, including Azure public-facing services, is done by Public IP Addresses
These IP addresses can be allocated in one of the following ways,
- Static Allocation
- Dynamic Allocation (default)
Private IP Address
Private IPs are assigned to resources, dynamically by Azure-provided Dynamic Host Configuration Protocol (DHCP). An IP address that is allocated by DHCP has an infinite duration and is released only if the resource is deallocated (stopped).
Static Private IP Address
Static Private IP addresses can be configured from the range of IP addresses defined within the Vnet, which are reserved for specific VMs.
Static private IP addresses are typically used for:
- VMs that act as domain controllers or DNS servers.
- Firewall rules are applied to the resources that are using IP addresses.
- The other apps/resources can access the resources through an IP address.
Dynamic IP is allocated by default to the VM from the subnet via DHCP. When VM is started/stopped, the IP may be released/renewed based on the DHCP lease
Public IP Address
Azure resources such as VM, Vnet Gateway, etc that need Inbound and Outbound Internet connectivity with external resources are allocated to Public IP addresses.
A public IP address is allocated dynamically from a pool of available IP addresses in the Azure Datacenter IP Ranges.
It is allocated to the associated resource like a VM or load balancer, when they are created, and released when the resource is stopped (or deleted).
Static Public IP Address
Static Public IP addresses can be configured and associated with a load balancer, application gateway, or a network interface card of the VM. It can not be changed and is released only when the resource gets deleted.
Static public IP addresses are commonly used when:
- To communicate with your Azure resources end-users need to update firewall rules.
- The scenario where a change in IP address would require to update A records is `DNS name resolution
- You use SSL certificates linked to an IP address.
- The apps or services that use an IP address-based security model can communicate with Azure resources.
Limitations of Using these IP Addresses !!
There are a few IP address ranges that are not allowed:
- 224.0.0.0/4: Multicast
- 255.255.255.255/32: Broadcast
- 127.0.0.0/8: loopback
- 169.254.0.0/16: link-local
- 168.63.129.16/32: Internal DNS
With this, we come to the end planning phase for Vnets. By now, you should be familiar with planning and configuring Private and Public IP Addresses.
In the next section you will learn about planning and implementation of Azure DNS, which should equip you to be able to plan and configure a Vnet .
What Is An Azure DNS ?
It does translate the service names, for example, a website to an IP address. Azure provides DNS as a service by which you can host your domains in Azure .
- DNS domains can be hosted on Azure’s global network of DNS name servers.
- It enables VMs and cloud services within Azure to communicate by name.
- Azure uses Anycast networking which provides both fast performance and high availability for the domain.
- Here Anycast networking means your DNS request is processed by nearby DNS server
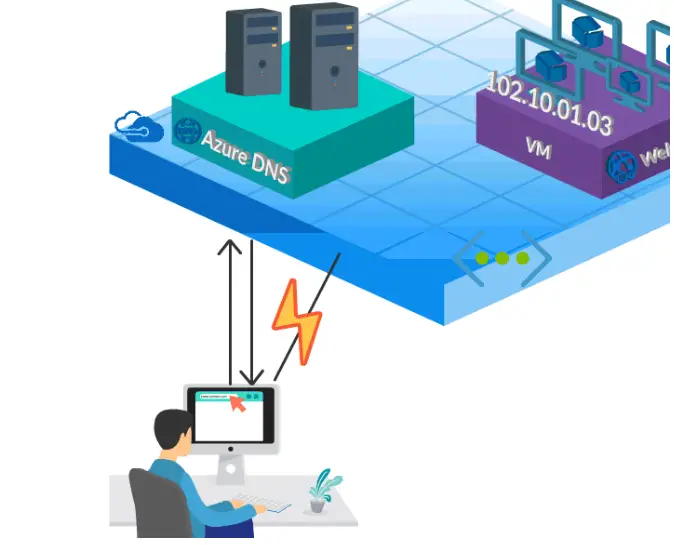
Planning of Name Resolution
Azure DNS provides name resolution for:
- VMs in the same cloud service:
- VMs in the same VNet.
- VMs in different cloud service but within a single VNet using FQDN (Fully Qualified Domain Name).
Own DNS can be used for name resolution:
- Between VMs in a VNet and on-premises computers.
- Between VMs in different VNets.
- Between on-premises computers and public endpoints.
DNS Zone In Azure Network !!
Domain is a unique name in the DNS, for example, ‘facebook.com’.
DNS zone is like a container for the records for a specific domain. The zone name and domain name remains the same.
For example, the domain ‘facebook.com’ may contain a number of DNS records such as ‘mail.facebook.com’ (for a mail server) and ‘www.facebook.com’ (for a website). Azure DNS helps manage DNS zone and DNS records for a domain.
Azure Reverse DNS Zone
Reverse DNS zone is one of the most important features of DNS service. Reverse DNS functionality is totally reverse to the DNS functionality. It does translate the IP Addresses to the domain names.
It’s commonly known to create a classless reverse DNS zone in a DNS server and instead of keeping a forward slash, you will keep “Hyphen” in creating reverse DNS zone.
Private Azure DNS zone
The tasks that are done Azure DNS zone are also done by the private azure DNS zone but in a customized way.
To use private DNS zones, you need to send your subscription details to AzureDNS-PrivateZone@microsoft.com, as it is available in preview currently.
You can create a Private Azure DNS zone for the virtual network queries and another zone for internet-facing queries.
DNS Records In Azure Network
A DNS record is created by the following syntax
Record.DomainName
An Azure DNS zone can support all common DNS record types as below,
- A or AAAA: Host – Maps hostname to IP address such as
webapp1.xxx.comto 104.10.10.10. - CNAME: Maps one host record to another host record to the same domain or other domain
- MX: Points to mail servers in the domain.
- NS: Delegates a DNS zone to the specified authoritative name server.
- SOA: Points the authoritative record for the zone.
- SRV: Identifies hosts that are providing specific services`**.
- TXT: Records the human-readable text field in DNS.
Types of DNS Servers
Authoritative DNS server hosts DNS zones. It answers DNS queries for the records in those zones only.
Recursive DNS server does not host DNS zones. DNS queries can be answered by calling authoritative DNS servers to collect the relevant data. The default DNS service provided by Azure DNS is Authoritative DNS service
Azure DNS Delegation
Azure DNS can be delegated in two ways :
- Domain Delegation
- Sub Domain Delegation
You can host a DNS zone and manage the DNS records for a domain in Azure. It is not a domain registrar.
Domain Delegation is done by creating a DNS zone in Azure DNS and setting up the NS records for a child zone in a parent zone.
Setting Up Delegation
- When delegating a domain to Azure DNS, you must use the name server names provided by Azure DNS.
- Use all 4 name server names, irrespective of the name of your domain.
NOTE : you need not own a domain to create a DNS zone in Azure DNS. But you have to own the domain name if you want to set up the delegation to Azure DNS with the domain registrar.
Internet domain names can be provided, verified and allowed to you by a company known as Domain Registrar
Distributing Network Traffic In Azure !!
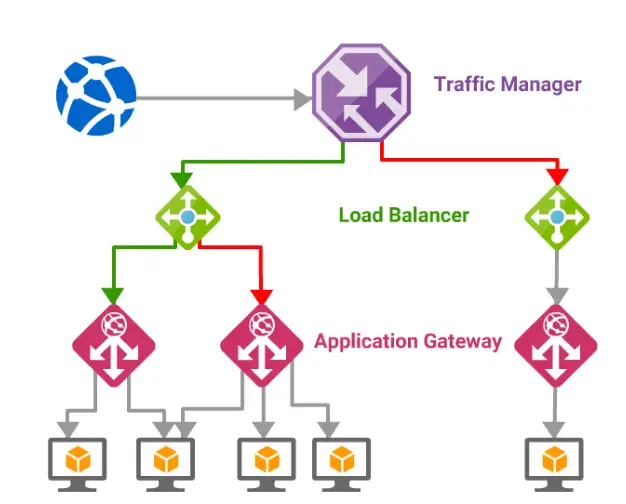
You can distribute network traffic in Azure in three different ways. Each of these ways work differently and support different scenarios. They can be used in isolation or in combination.
- Azure Load balancer: Provides network-level distribution of traffic across instances of the application running in the same Azure Datacenter
- Traffic Manager: This essentially works at DNS level and uses DNS Responses to direct end-user traffic to globally distributed Endpoints
- Application Gateway: Works at Application Layer and acts as a reverse proxy service . This terminates the client connection and forwards request to back endpoints.
- In traffic management, need for balancing resources and high availability are critical.
Azure Load Balancers In Azure Virtual Network !!
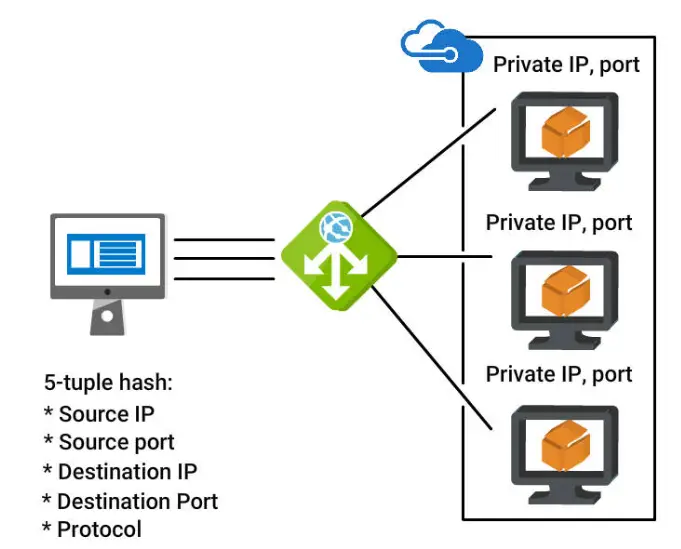
It is a Layer 4 (transport) routing option or in other words, it can be described as properly routing TCP or UDP traffic.
It supports routing for virtual machines and cloud services. It supports virtual and hybrid networks (On-premises and Azure cloud). Reserved IP address is supported in port forwarding .
Routing a session is based on 2 rules
- Hashing or tuple of IP addresses.
- ports and protocols
There are two types of load balancers such as
- Internet-facing load balancer
- Internal load balancer
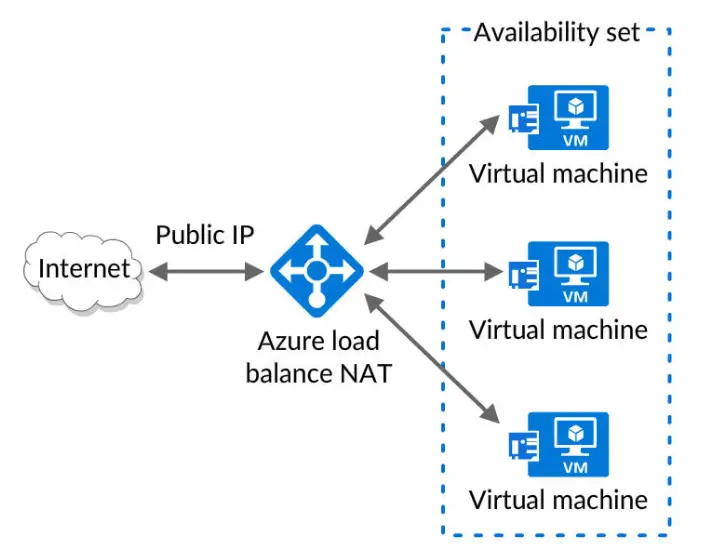
What is Internet Facing Load Balancer In VNet ?
Load balancer passes public IP request to the virtual machine and the virtual machine response is routed back to the client through the public load balancer onto the public IP.
By applying load-balancing rules, you can distribute specific types of traffic across multiple VMs or services .
What Is Internal Load balancer In Azure VNet ?
Azure Internal Load Balancer (ILB) directs traffic to resources that are inside a cloud service or that use a VPN to access Azure infrastructure.
ILB enables load balancing:
- Set of VMs within a cloud service
- Set of VMs within a Vnet
- For line-of-business applications hosted on Azure
- For a cross-premises virtual network- Load balancing from on-premises computers to a set of VMs that lies in the same cloud of the Azure virtual network
- For a cross-premises virtual network –
- Among tiers in a multi-tier application
Load Balancer Features In Azure
Load Balancer supports the following features.
- Hash-based distribution
It uses a 5-tuple – source IP, source port, destination IP, destination port, and protocol type
5-tuple hash used to map traffic to available servers.
It provides stickiness only within a transport session.
Packets in the same TCP or UDP session will be directed to the same IP instance behind the load-balanced endpoint.
- Port Forwarding
The control is represented through endpoints in Load Balancer.
Endpoint listens to a public port and forwards the traffic to an external port
The endpoint can have the same port number for public port and external port or different.
- Service Monitoring
The load balancer can probe the health of the various server instances to distribute the traffic
- Outbound Connections
The private IP address of a virtual network or virtual machine of an Azure cloud is communicated to the public IP address of the internet can be done by translating the public IP address of a Load Balancer .
Azure Traffic Manager
Traffic Manager is another type of load balancer distribution.
By using the traffic manager you are distributing traffic of various service endpoints across multiple Azure data centers and multiple regions across the world.
It supports various endpoints, such as cloud services, App Services, and even public IP addresses that are associated with VMs, Load Balancers, and so on.
It also uses non-Azure endpoints, either in other clouds or in your on-premises environment
Azure traffic manager uses DNS to specify the endpoint.
Traffic Manager benefits In Azure
High availability – Traffic manager makes sure that client request is going directly to the healthy endpoint.
Better responsiveness – It can distribute the traffic across different datacentres in the world and also ensures that it directs traffic to the nearest endpoint.
Maintenance with zero downtime – you can also redirect the traffic to other endpoints and make sure that they are running properly and efficiently.
Distributing across Azure and external endpoints – You can also distribute traffic to other clouds or to your premises.
Azure Traffic Manager – Routing Methods
Traffic Manager receives DNS query from the client and it doesn’t direct the request directly to Endpoint.
It checks for routing method which is being used and based on that it will choose the service endpoint to direct the client request.
Azure Traffic Manager follows 4 routing methods:
Performance: It routes the client queries to the nearest endpoint based on the geographic location to the client.
Weighted: It routes the client queries based on a weight that you define.
Priority: The request is sent to the primary service endpoint if it goes down it is redirected backup service endpoint.
Geographic: It detects the region from which the DNS query is originated and redirects it to a specific endpoint.
What Is Azure Application Gateway In Any Azure VNet ?
Application Gateway(AG) is a layer 7 load balancing service for applications. This service comes with many features for customers using web applications, such as SSL and CPU offloading.
Application Gateway Features
Capabilities of Application Gateway:
Web application firewall – It provides protection for web applications and helps in prevention of malicious attacks.
WebSocket support – For example, if your web application wants a stateful connection to a client such as a web chat application you can keep your WebSocket driven components behind an application gateway.
HTTP load balancing – client requests are routed round-robin meaning each HTTP based service that is set to respond to a specific URL will have an equal chance of handling a request.
Cookie-based session affinity– – In cases like the shopping-cart traffic must be routed to the same VM where they follow session affinity via cookies.
Secure Sockets Layer (SSL) offload – AG will provide you with end-to-end SSL processing and applications that want to free web server farms from SSL termination overhead.
Application Gateway Types
There are two types of application gateways
1. Standard – All the features are available in this gateway except for the protection and prevention of attacks.
2. Web Application Firewall(WAF) – It provides all the features available in standard and in addition it gives protection from attacks and web vulnerabilities prevention.
This software protects you against the most common forms of web attacks such as sequel injection and cross-site scripting known BOTS and scanners problems with each HTTP request such as forgeries protocol violations.
Hope you really liked this detailed post regarding Azure virtual network . Stay tuned for more interesting stuff in this series .
Aric is a tech enthusiast , who love to write about the tech related products and ‘How To’ blogs . IT Engineer by profession , right now working in the Automation field in a Software product company . The other hobbies includes singing , trekking and writing blogs .